Navigating Travel Industry Risks with Intelligent Communications
We’re going to explore some real-life unforeseen circumstances that the travel industry has had to navigate and how intelligent communications solut...
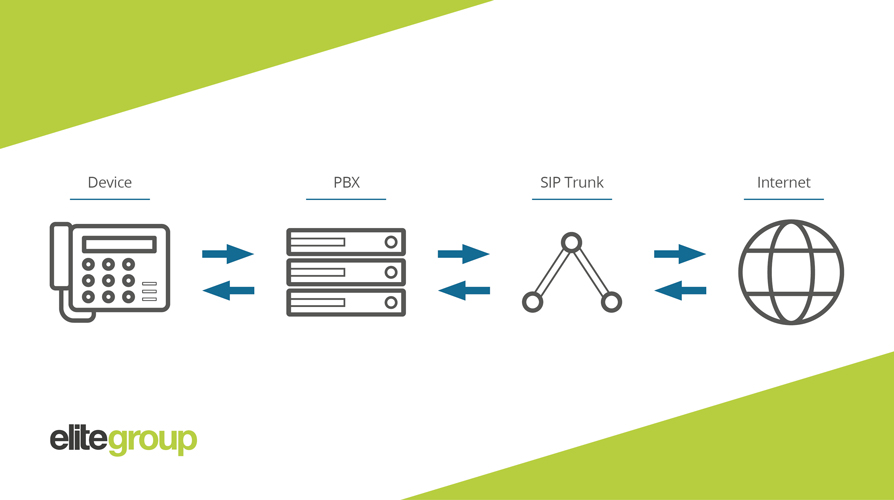
When moving your communications over to VoIP (Voice over Internet Protocol), your solutions will rely on SIP (Session Initiation Protocol). This is the technology that makes and completes voice calls in most VoIP solutions, including calls that are being placed via your business phone system, smartphone or through an app. By itself, SIP technology isn’t secure and can be easily hacked if not bolstered by sound security processes and solutions.
Knowledge is power, so we’re going to outline everything you need to know about five of the most common SIP security risks and how to avoid them by following SIP security best practice. By the end of this article you’ll be able to make the move to VoIP communications via SIP with the confidence that your data will remain protected.
Gaining an understanding of what risks your SIP technology faces, places you in a better position to protect yourself by implementing the right security solutions.
Also known as Caller ID spoofing, this method is used to carry out impersonation fraud and to deploy spam, often using pre-recorded messages. Hackers alter the caller ID, often by making it appear as a local number, to trick the receiver into answering the call. The receiver will then hear the message, which is usually modelled to sound like a legitimate organisation, such as a bank or HMRC, in order to gain sensitive information, such as financial details.
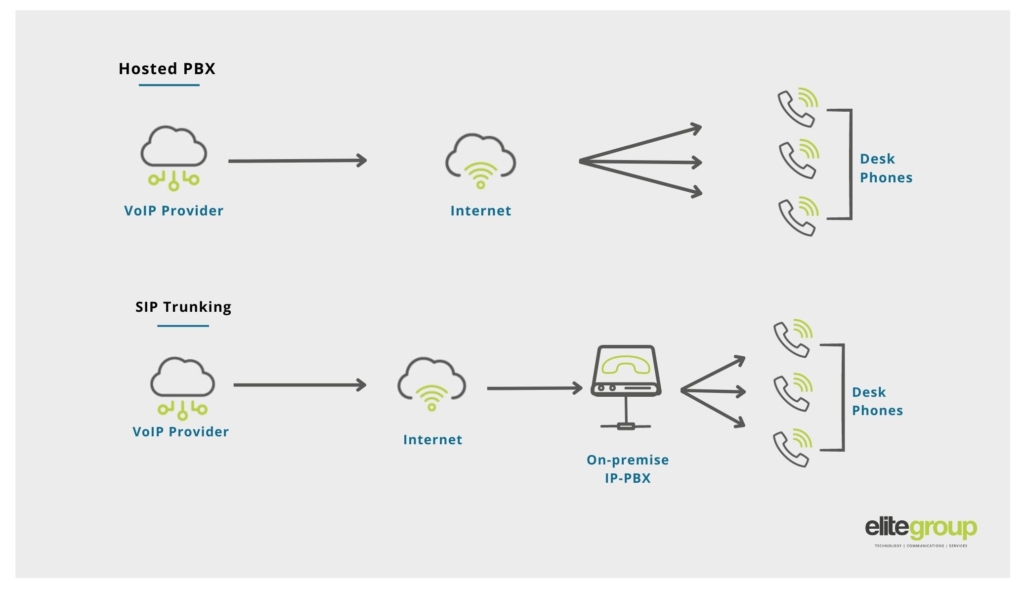
As the name suggests, PBX hacking involves criminals hacking into a business’s PBX (the private telephone network that handles your communications) and manipulating it in a way that costs your company money. Criminals can also use this technique to attempt to steal data or cause the network to become unusable. Even companies that have moved away from traditional PBX to IP PBX are at risk, as criminals have adapted their methods to attack this newer technology.
Wangiri is a Japanese term that means ‘one (ring) and cut’ and this method is used to trick you into calling a premium rate number. The criminal will leave a missed call on several phones. Once the user receives the notification that they’ve missed the call and calls the number back, they will be re-routed to a premium-rate number and will be charged for the expensive call.
IRSF is where attackers collaborate with telecom operators and premium rate service providers to artificially increase traffic to international premium rate numbers. Part of the revenue raised from this type of fraud will be shared from the telecom providers with the fraudsters who initiated the call.

Now we’ve covered some of the most common security risks, it’s time to learn how you can defend your SIP technology against them.
TLS 1.3 is the latest version of the internet’s most deployed security protocol. It works by encrypting data to provide a secure communication channel between two endpoints. TLS 1.3 is faster and more secure than previous versions of this protocol and is less vulnerable to cyber attacks. When placing a call, the TLS 1.3 protocol will encrypt the data sent via VoIP communication by securing SIP traffic in and out of a communication system.

Most cyber attacks target endpoints of a network. Therefore, implementing a Firewall in front of end-point devices within your communication system, such as handsets and/or computer running softphones via an app can help to reduce security threats to a VoIP connection.
Integrating Firewalls within your SIP solution adds another layer of protection when transmitting data via VoIP communications. This will be a Firewall that is configured to your solution to ensure high quality calls that are protected and safeguard your internal network, as well as external calls.
This security solution allows a SIP provider to analyse the IP address that a call request is coming from and provide access for this IP address if it is on the list of trusted addresses. This method is only advantageous for fixed IP addresses, so is most suited to on-site PBX servers, rather than hosted or cloud PBX that are accessed via mobile or wireless networks.
So, we’ve covered common risks and top solutions for ensuring your SIP technology is defended. The last topic we need to cover is SIP security best practices, which will ensure that all users and processes within your business are doing their part to keep your communications secure.
Yes, keeping on top of software updates can be a pain – we sympathise! However, one of the biggest causes of security breaches is out-of-date software. Updates carry vital changes and improvements that safeguard your data and missing these updates can leave holes that allow your information to become vulnerable to criminals.
Did you know that the average employee reuses the same password up to 13 times across different systems? Why is this a statistic that would keep an IT team up at night? Once this password has been compromised by a criminal, they will then try it across other logins, leaving many of the applications that rely on this password wide open. Ensure all users within your business are employing good password management, including using unique, complex passwords for each of their logins across systems, apps and programmes.
Before going ahead and signing a contract with a SIP trunk provider, ensure you’ve checked out their security processes and accreditations in detail. Your provider should be able to take you through the security measures your solution includes and also the steps they take to safeguard your data including accreditations, such as ISO.

Equip your business with a resilient, secure internet-based communications solution with SIP trunk solutions from Elite. When it comes to security, you can rely on fraud protection enabled within your SIP trunk service as standard, providing rapid response and notifications should a fraud attempt occur. You can enjoy all the benefits of digital communications, whilst having peace of mind that your data security is guaranteed with a trusted Calling Line Identification (CLI) and dedicated IP address with full monitoring for suspicious activity provided.
Contact us today and let’s work together to level up your communications with a secure SIP trunk solution today.